In my years writing about cybersecurity, I’ve realized one common reality: nobody wakes up enthusiastic about id and entry administration (IAM), however everybody regrets ignoring it.
Between workers reusing weak passwords, phishing makes an attempt focusing on credentials, and the rising net of SaaS purposes, maintaining accounts safe with out irritating customers is simpler mentioned than completed.
Throw in distant work, third-party integrations, and compliance audits into the combo, and it’s no shock that IAM appears like an infinite sport of catch-up. The problem isn’t nearly safety — it’s about discovering the proper IAM device that really works with out including complexity to each day operations.
Should you’re a safety chief, IT supervisor, or enterprise decision-maker, discovering the finest id and entry administration software program in your group can really feel overwhelming. With so many choices promising hermetic safety and seamless integration, how are you aware which one actually delivers?
I’ve completed all this analysis, so that you don’t must. I spoke with IAM consultants, reviewed G2 reviews, and gathered insights from my very own IT and safety group (who’ve seen sufficient unhealthy IAM setups to final a lifetime). After evaluating 15 main IAM options, I’ve narrowed it all the way down to the highest 5 that really stand out for safety, scalability, and usefulness.
5 finest id and entry administration software program: My High Picks
- Microsoft Entra ID: Greatest for organizations already within the Microsoft ecosystem
Seamless integration with Azure, Workplace 365, and Intune, with sturdy conditional entry insurance policies. ($6/consumer/month) - JumpCloud: Greatest for multi-OS id administration with built-in MDM Unified platform combining IAM, MDM, and listing providers for Home windows, macOS, Linux, iOS, and Android. ($9/consumer/month)
- Okta: Greatest for enterprise-grade authentication and SaaS integrations
Versatile SSO and adaptive MFA that integrates with 1000’s of apps throughout multi-cloud environments. ($2/consumer/month for SSO) - Salesforce Platform: Greatest for companies working on Salesforce
Constructed-in SSO, MFA, and buyer id options with customizable entry insurance policies inside Salesforce. ($5/consumer/month) - Cisco Duo: Greatest for easy, safe MFA and SSO
Simple-to-use authentication with Duo Push, adaptive insurance policies, and a free plan for small groups. ($3/consumer/month)
*These are the top-rated merchandise within the IAM software program class, in keeping with G2’s Winter 2025 Grid® Report. I’ve talked about the beginning value of their paid plans for simple comparability.
Whether or not you’re upgrading your IAM technique or trying to decide on the main id and entry administration platform for the primary time, this information will aid you discover the perfect match in your group.
5 finest id and entry administration software program I like to recommend
With out IAM, managing consumer entry is like handing out keys to an workplace and shedding monitor of who has them or the place they’re getting used. It’s what retains that chaos in verify.
IAM protects entry, whereas operational danger administration software program helps tackle the dangers tied to these identities throughout the enterprise. It controls who will get entry to what, when, and the way securely, so IT groups can implement safety insurance policies, stop unauthorized entry, and scale back danger with out turning each login try right into a assist ticket.
I’ve researched my fair proportion of IAM software program in all sizes and styles, from cloud-focused ones to on-premises options and from extremely customizable techniques for giant enterprises to easy choices for rising groups.
From my analysis and conversations with IAM consultants, I’ve realized that the perfect IAM software program isn’t nearly safety. It is concerning the steadiness between safe consumer authentication, granular entry controls for implementing the least privilege, and clean integration with current techniques.
And the stakes are solely getting greater. The worldwide IAM market is projected to succeed in $41.52 billion by 2030 from $15.93 billion in 2022.
How did I discover and consider the perfect IAM software program?
Discovering the perfect IAM software program isn’t nearly evaluating characteristic lists or vendor guarantees — safety leaders want options that really work in the true world. I began by analyzing G2 Grid reviews, which rank IAM instruments primarily based on real-world adoption, consumer satisfaction, and enterprise match. This gave me a transparent view of which platforms dominate the house and the way they carry out in areas like authentication, entry management, and compliance.
To transcend rankings, I used AI to investigate a whole bunch of consumer opinions of those merchandise. This helped me establish recurring themes — whether or not it was frustration over clunky authentication flows, reward for adaptive entry insurance policies, or considerations about integration with current safety stacks.
Given I couldn’t enroll and entry the device myself, I additionally spoke with IAM consultants, my very own IT and safety group members, and professionals who take care of id safety each day and use these instruments and validated their feedback with verified G2 opinions. Their suggestions helped me lower via the noise and concentrate on options that ship sturdy safety with out changing into a bottleneck for IT operations.
The screenshots featured on this article could also be a mixture of these captured throughout testing and ones obtained from the seller’s G2 web page.
Do you know? On common, companies report ROI on IAM investments in 14 months, in keeping with G2 Information.
What makes the perfect id and entry administration software program: My standards
Primarily based on every little thing I’ve realized, right here’s the guidelines I used to judge the highest IAM resolution:
- Sturdy authentication with out friction: Authentication needs to be strong, however it shouldn’t create pointless complications. If logging in appears like a chore, customers will take shortcuts — reusing passwords, writing them down, or bypassing safety altogether. I regarded for IAM options that supply multi-factor authentication (MFA) past the fundamentals, with choices like biometric verification, passwordless login, and adaptive authentication that adjusts safety necessities primarily based on danger. Single sign-on (SSO) was one other massive issue because it reduces login fatigue whereas sustaining safety. Threat-based authentication additionally stood out — options that analyze habits, location, and machine to set off extra safety when wanted scored greater on my record.
- Granular entry controls and role-based administration: It’s not nearly who can log in — it’s about what they will entry as soon as inside. IAM options that supply sturdy role-based entry management (RBAC) made the lower, permitting IT groups to handle permissions at scale with out manually adjusting each consumer’s entry. I additionally checked out instruments with attribute-based entry management (ABAC), which considers context like machine kind, location, and login habits to make smarter entry choices. Simply-in-time entry was one other characteristic that stood out, limiting high-privilege entry solely when it’s completely essential, decreasing long-term publicity to delicate techniques.
- Integration with current safety infrastructure: An IAM system isn’t helpful if it doesn’t match into the broader safety ecosystem. I prioritized options that combine easily with id suppliers like Energetic Listing and Azure AD, in addition to SIEM platforms for real-time authentication monitoring. IAM also needs to join with HR and ITSM techniques for automated provisioning and de-provisioning of accounts — as a result of guide account administration is a recipe for errors and safety gaps.
- Compliance and audit-readiness: For organizations coping with strict laws, IAM isn’t only a safety device — it’s a compliance requirement. I centered on options that supply built-in audit logs, detailed compliance reporting, and governance options like entry opinions and certification workflows. Assembly trade requirements like SOC 2, ISO 27001, HIPAA, and GDPR was one other main issue. Safety leaders want IAM instruments that don’t simply assist them safe identities but in addition make compliance audits much less of a nightmare.
- Scalability and suppleness for rising organizations: A great IAM resolution ought to develop with the enterprise, not maintain it again. I evaluated how nicely these instruments assist hybrid IT environments and whether or not they supply multi-tenant assist for enterprises managing a number of subsidiaries or divisions. API-driven customization was one other key issue — organizations want IAM techniques that permit them to automate workflows and combine with different safety instruments as an alternative of forcing a inflexible, one-size-fits-all method.
- Person expertise: IAM safety solely works if individuals really use it. I regarded for IAM options that supply clear, intuitive admin dashboards that IT groups can navigate with out intensive coaching. Self-service password reset was one other main issue — IT groups don’t have time to continuously unlock accounts simply because somebody forgot a password. One of the best options scale back friction whereas nonetheless implementing sturdy safety insurance policies.
After checking every device in opposition to this guidelines and cross-referencing it with knowledgeable insights, real-world suggestions, and AI-driven evaluation evaluation, I recognized the highest 5 IAM options.
Whether or not you are in search of the perfect id administration device with multi-factor authentication, or the perfect IAM software program for securing distant workforces, there is a device beneath.
The record beneath accommodates real consumer opinions from the IAM software program class. To be included on this class, an answer should:
- Provision and de-provision of consumer identities.
- Assign entry primarily based on particular person position, group membership, and different elements.
- Implement consumer entry rights primarily based on permissions.
- Confirm consumer id with authentication, which can embody multi-factor authentication strategies.
- Combine with directories that home worker information.
*This information was pulled from G2 in 2025. Some opinions might have been edited for readability.
1. Microsoft Entra ID: Greatest for organizations already within the Microsoft ecosystem
From what I’ve seen in G2 opinions, Microsoft Entra ID (previously Azure Energetic Listing) is usually highlighted as one of many main id and entry administration platforms, largely because of its deep integration into the Microsoft ecosystem. Many customers respect how seamlessly it really works with different Microsoft providers like Azure, Dynamics 365, Intune, and Energy Platform.
I’ve observed that G2 customers continuously point out how Entra ID comes included at no extra price if your organization is already utilizing Microsoft providers. This built-in assist for MFA, limitless SSO throughout SaaS apps, fundamental reporting, and self-service password modifications is a serious benefit, significantly for companies which are already built-in into the Microsoft surroundings.
From my analysis, I’ve discovered that Entra ID’s sturdy authentication and safety controls stand out to many IT professionals. The flexibility to implement versatile conditional entry insurance policies, particularly when paired with Intune for endpoint administration, is usually praised as a complete resolution for unified entry management.
I’ve seen a number of G2 customers categorical their appreciation for conditional entry, which permits IT groups to tailor safety insurance policies primarily based on consumer habits, location, and danger ranges. This performance is very valued as a result of it helps steadiness safety with usability, prompting MFA for unrecognized gadgets whereas permitting trusted gadgets to entry assets with minimal friction.
One characteristic that customers continuously name out is Entra Join, which permits seamless integration of on-premises Energetic Listing with Entra ID. I’ve learn a number of opinions from organizations transitioning to the cloud who discover this significantly helpful for simplifying entry administration throughout each cloud and on-premises infrastructures.
That being mentioned, setup and configuration are frequent ache factors I famous amongst G2 reviewers, particularly for companies with combined IT environments. A number of reviewers observe the time and complexity required to get every little thing working easily, significantly when migrating from non-Microsoft setups.
Licensing prices was one other recurring theme in G2 suggestions I noticed. Whereas Entra ID provides a free tier, customers typically point out that the extra superior security measures, reminiscent of these below id safety, governance, and privileged entry administration, are solely out there in higher-tier licenses like Entra ID P2.
From my evaluation, small companies typically wrestle with the price of premium licensing regardless of needing superior options. Many G2 customers have shared that determining which Entra ID tier most closely fits their wants may be tough when balancing safety and compliance necessities.
General, regardless of the challenges, I’ve seen a basic consensus that Microsoft Entra ID is a stable IAM resolution. For giant organizations deep in Microsoft, it’s typically the reply to “which id entry app is finest for enterprises?”
What I like about Microsoft Entra ID:
- I’ve seen G2 customers reward how Entra ID integrates seamlessly with Azure, Workplace 365, and different Microsoft providers, making SSO and conditional entry clean and easy.
- I’ve additionally observed that hybrid id administration with Entra Join is a standout characteristic, particularly for companies nonetheless sustaining on-premises infrastructure, simplifying the sync between on-prem Energetic Listing and the cloud.
What G2 customers like about Microsoft Entra ID:
“Microsoft Entra is without doubt one of the finest options Microsoft provides for verifying and figuring out enterprise know-how belongings reminiscent of laptops and cellphones. It ensures that solely the proper individuals have entry to particular assets.
What I like essentially the most are these three options: multi-factor authentication with the Microsoft Authenticator app, id administration for every machine, and its integration with BitLocker, which supplies full disk encryption for the asset. This fashion, information is securely saved and may be recovered with a BitLocker restoration key.”
– Microsoft Entra ID Evaluation, Erick Vincent Steve G.
What I dislike about Microsoft Entra ID:
- From what I noticed, establishing Entra ID isn’t precisely a clean trip. G2 customers who aren’t in Microsoft’s ecosystem took some additional effort and time to get every little thing configured correctly.
- Primarily based on my analysis, licensing price is one other ache level. G2 customers report that the free tier covers the fundamentals, however a few of the options that safety groups really want are locked behind Entra ID P2, which isn’t low-cost.
What G2 customers dislike about Microsoft Entra ID:
“Customers unfamiliar with Microsoft merchandise will face difficulties in understanding the combination of this product, and the identical goes for corporations utilizing non-Microsoft platforms. The price of implementing Microsoft Entra ID may very well be a priority for low-budget corporations together with this, the businesses that pose challenges in environments with unstable web entry can face issues as a result of Entra ID is cloud-based.”
– Microsoft Entra ID Evaluation, Sahil C.
2. JumpCloud: Greatest for multi-OS id administration with built-in MDM
From what I’ve seen in G2 opinions, JumpCloud is usually praised for being a versatile, cloud-first IAM resolution designed for organizations shifting away from conventional on-prem id administration.
Many customers respect its skill to handle identities throughout a number of platforms, together with Home windows, Android, iOS, macOS, and Linux, all from a single platform. This open listing method permits it to combine seamlessly not solely with Azure or Energetic Listing but in addition with Google Workspace, AWS, and different third-party SaaS apps, making it an interesting alternative for multi-cloud and hybrid setups.
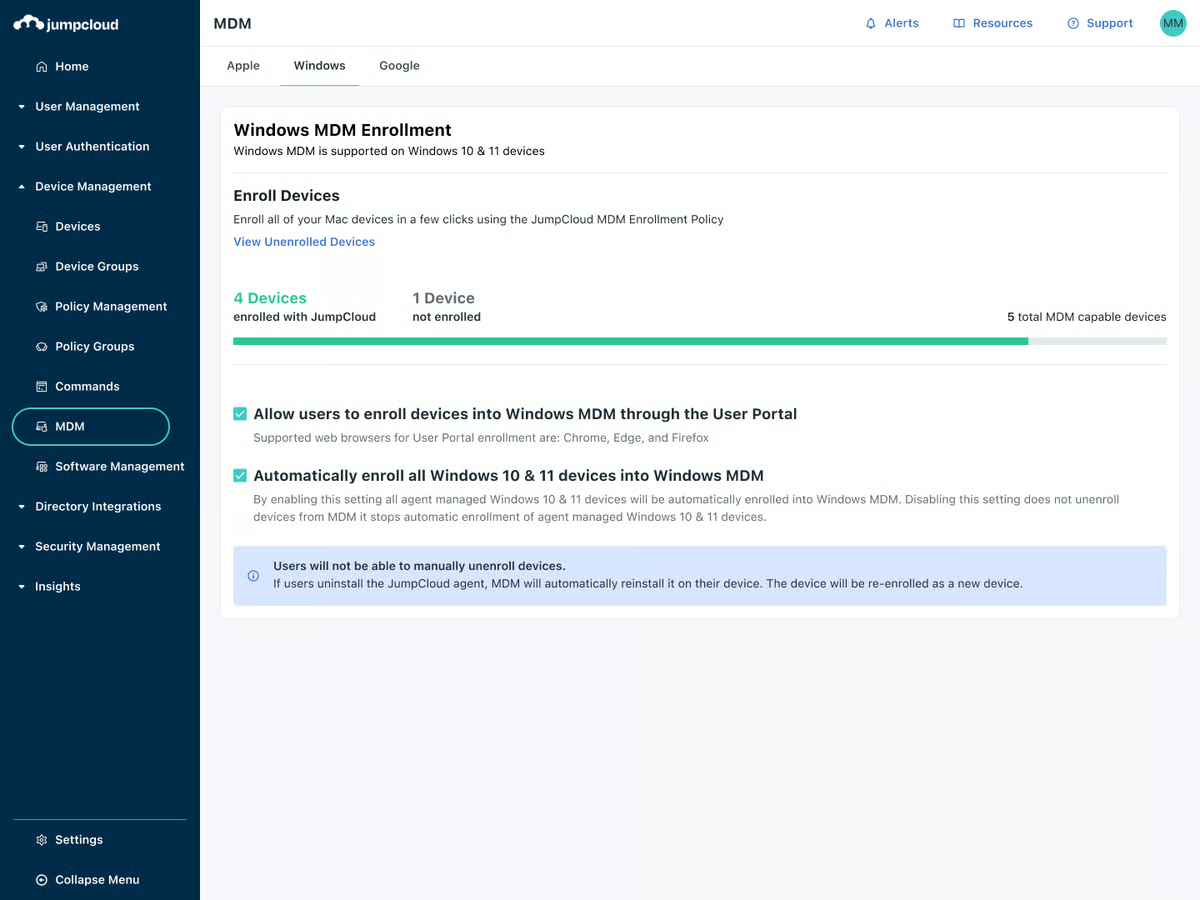
I’ve observed that G2 customers spotlight JumpCloud’s all-in-one platform, which mixes IAM, cell machine administration (MDM), listing providers, and endpoint safety. This integration makes managing customers, gadgets, and safety insurance policies from a single platform significantly engaging to IT groups juggling a number of working techniques. Many customers report vital time financial savings and streamlined operations due to this unified method.
From a usability standpoint, I’ve seen a number of opinions commending JumpCloud for its clear and user-friendly interface. Customers discover the onboarding course of easy, and the flexibility to simply deploy SSO and MFA throughout the group is extremely valued.
One characteristic that’s continuously talked about in G2 suggestions is JumpCloud’s intensive information base, which incorporates step-by-step tutorials and movies. Many customers respect this useful resource for making setup and implementation simpler. Moreover, JumpCloud’s buyer assist receives constructive opinions for being dependable and responsive when points come up.
Nonetheless, some G2 customers do level out sure lacking options. As an example, the dearth of self-service for account unlocks signifies that IT groups should manually help customers who’re locked out, which might turn out to be cumbersome. Distant help is one other space the place some customers observe points, because it’s seen as considerably clunky and in want of enchancment.
I’ve additionally seen a number of G2 opinions point out that JumpCloud’s MDM capabilities, whereas helpful, might not present the identical degree of granular management and automation present in different MDM options, particularly in Apple-heavy environments. Customers managing giant fleets of gadgets, significantly Apple gadgets, typically really feel that JumpCloud doesn’t fairly match as much as specialised MDM options like Jamf.
Regardless of these drawbacks, I imagine JumpCloud’s predominant energy is its unified method to IAM, listing providers, and MDM.
It provides an all-in-one resolution that works nicely for small and medium companies, regardless that it’d come at a better value level than standalone enterprise-grade IAM or MDM options. That’s why I think about JumpCloud the most effective IAM options for mid-sized tech corporations juggling a number of platforms. For organizations in search of an built-in platform, JumpCloud stays a stable choice.
What I like about JumpCloud:
- From what I’ve seen in G2 opinions, JumpCloud provides flexibility by managing identities throughout Home windows, macOS, Linux, Android, and iOS from one platform, not like Microsoft Entra ID, which is extra optimized for Microsoft environments.
- I’ve observed that JumpCloud combines IAM, cell machine administration (MDM), listing providers, and endpoint safety, which simplifies IT administration throughout completely different working techniques.
What G2 customers like about JumpCloud:
“JumpCloud may be very simple to make use of and user-friendly. It helped us handle our workers’ techniques. We are able to now handle software program software installations on these techniques through a characteristic in JumpCloud, Software program Administration, which is kind of useful.
Additionally, it is extremely simple to use any insurance policies through JumpCloud to end-user techniques, reminiscent of password coverage, MFA for logging into the system, and so forth. Additionally, listing integration may be very simple to arrange, reminiscent of AD, Cloud, or HR directories. With this, we are able to additionally run instructions on distant techniques and take distant help/management of the system, which may be very helpful. And the client assist is all the time there for you, and they’re fairly quick in responding.”
– Jumpcloud Evaluation, Saurabh R.
What I dislike about JumpCloud:
- I’ve discovered that self-service account unlocks are lacking, which means IT should step in each time a consumer is locked out, which different IAM options typically permit customers to deal with on their very own.
- I’ve additionally learn that distant help feels clunky, and MDM, whereas useful, doesn’t present the identical granular management and automation as instruments like Jamf, particularly for Apple-heavy environments.
What G2 customers dislike about JumpCloud:
“Jumpcloud has but to develop superior options like self-service for Account unlocks, Person orchestration, and governance capabilities, that are essential on this period of enterprise safety administration.“
– Jumpcloud Evaluation, Gangadhara S.
Controlling who accesses your techniques is one a part of the puzzle. Managing the gadgets they use is the following. Discover the finest Cellular Gadget Administration (MDM) options I belief to maintain each endpoint safe, up to date, and compliant.
3. Okta: Greatest for enterprise-grade authentication and SaaS integrations
Okta is without doubt one of the most versatile and scalable IAM options, particularly for organizations requiring sturdy safety and superior authentication. Like JumpCloud, it’s vendor-neutral and works nicely in multi-cloud environments and with complicated SaaS integrations.
I’ve observed that Okta integrates seamlessly with instruments like Microsoft, Google Workspace, and AWS, making SSO, adaptive authentication, and automatic consumer provisioning easy throughout a variety of purposes.
From a consumer expertise standpoint, I’ve discovered Okta’s interface intuitive for each IT groups and finish customers. It’s continuously praised for providing one of many smoothest SSO experiences.
I additionally worth that Okta helps third-party MFA and token suppliers and its personal built-in MFA, giving corporations the flexibleness to combine no matter works finest for them. The customizable SSO portal is one other characteristic that stands out for simplifying app administration.
With regards to dealing with scale, Okta is usually seen as the highest id administration service for startups aiming to develop quick with out safety bottlenecks.

Nonetheless, from what I’ve learn on G2, pricing generally is a barrier for smaller companies and startups, as Okta provides a la carte pricing, which might add up rapidly when a number of providers are wanted.
I’ve come throughout opinions the place customers talked about that establishing Okta may be difficult. Configuring insurance policies, settings, and integrations takes effort and time, which was overwhelming for some G2 reviewers. Whereas Okta supplies good documentation and assist, fine-tuning every little thing for optimum safety and automation nonetheless requires a substantial funding of time.
What I like about Okta:
- I worth how Okta integrates seamlessly with Microsoft, Google Workspace, AWS, and SaaS apps, making SSO, adaptive authentication, and consumer provisioning easy.
- I additionally like the flexibleness to customise SSO insurance policies and blend them with MFA choices like Okta Confirm, Symantec VIP, Duo Safety, and Google Authenticator, balancing safety and usefulness.
What G2 customers like about Okta:
“Through the years, I’ve labored with Okta throughout numerous corporations, and I need to say that it’s truthfully the most effective SSO options in the marketplace. Not solely is it user-friendly with a contemporary interface, however it additionally boasts high-security requirements and helps working with 1000’s of customers concurrently.”
– Okta Evaluation, Paloma G.
What I dislike about Okta:
- From what I noticed, the setup isn’t precisely fast. Okta is highly effective, however getting every little thing configured takes time. Many G2 reviewers reported that there are quite a lot of settings to fine-tune, and the training curve was steep.
- G2 reviewers point out the pricing as a draw back. In my view, it may also be a problem for smaller companies. With a minimal $1,500 annual contract, it might really feel out of attain for startups or small IT groups that solely want just a few core options.
What G2 customers dislike about Okta:
“Okta is dear and unsuitable for smaller companies. Pricing plans are a la carte and complicated. Configuring directories and consumer synchronization will take quite a lot of time and effort.”
– Okta Evaluation, Qual A.
4. Salesforce Platform: Greatest for companies working on Salesforce
Amongst CRM-heavy groups, Salesforce is a number one id and entry administration platform with built-in SSO and MFA. G2 customers typically spotlight as a robust IAM resolution, particularly for companies already working on the Salesforce Platform. Single Signal-On (SSO) and Multi-Issue Authentication (MFA) are two key options continuously talked about, with reviewers noting that these are important elements of the answer.
I’ve observed that many G2 customers respect Salesforce’s App Launcher. This allows customers to entry a variety of enterprise purposes — Salesforce apps in addition to third-party apps — without having to log in individually. Even when utilizing Energetic Listing for consumer administration, customers can depend on Id Connect with handle Salesforce accounts, which is seen as a big profit for usability and safety.
I’ve encountered noticeable satisfaction concerning Salesforce’s degree of management over information access. A number of reviewers point out how linked apps and OAuth allow fine-grained entry controls, permitting corporations to limit entry to delicate info. This is especially helpful for groups managing buyer accounts and delicate information.
From what I’ve learn, many G2 customers discover the Buyer Id characteristic to be a robust addition, particularly for giant companies that want to trace buyer exercise throughout a number of channels. Reviewers observe that the flexibility for purchasers to self-register, securely log in, and entry apps with a single id is a standout characteristic. The truth that it’s totally customizable to suit firm branding and workflows additionally helps companies streamline their processes.

Nonetheless, I’ve seen some customers observe the complexity of the setup course of. G2 reviewers continuously point out that configuring Salesforce Id may be time-consuming because of the giant variety of configurations, permissions, and integrations that have to be adjusted. This makes onboarding extra difficult in comparison with devoted IAM options like Okta or JumpCloud.
I’ve observed that some G2 customers report the platform may be barely sluggish at occasions, particularly when coping with giant datasets or complicated workflows. Whereas this isn’t seen as a dealbreaker, some reviewers have raised it, significantly concerning response occasions.
Lastly, I’ve learn a number of reviewers point out pricing as a consideration. Whereas Salesforce Id is usually seen as a very good match for bigger enterprises already inside the Salesforce ecosystem, G2 customers level out that it is probably not as budget-friendly for small to mid-sized corporations.
Primarily based on my evaluation of G2 opinions, Salesforce Id looks as if a stable choice for companies already closely invested in Salesforce, significantly these utilizing its CRM software program in Skilled, Enterprise, Limitless, or Efficiency Editions.
What I like about Salesforce Platform:
- I’ve seen that G2 customers discover Salesforce Id to be a pure extension of the Salesforce ecosystem, making it simpler to handle SSO, MFA, and consumer permissions inside one platform.
- I’ve observed that many reviewers respect the Buyer Id (CIAM) characteristic, permitting clients and companions to self-register and log in utilizing social sign-ins like Fb or LinkedIn.
What G2 customers like about Salesforce Platform:
“Salesforce is cloud-based and provides enterprise-grade scalability. Whether or not you are connecting to exterior techniques through APIs, utilizing Salesforce Join for exterior information sources, or leveraging pre-built connectors for in style instruments.
What I like finest about Salesforce is its flexibility and energy in enabling companies to construct customized purposes with out requiring quite a lot of complicated coding. Additionally, buyer assist is nice and really useful. I exploit Salesforce each day in my work. It’s simple to make use of, combine, and implement.“
– Salesforce Platform Evaluation, Rushabh U.
What I dislike about Salesforce Platform:
- From what I’ve learn, configuring Salesforce Id may be time-consuming. G2 customers point out that there are lots of settings and integrations to handle, making onboarding extra complicated.
- I’ve come throughout suggestions that processes may be sluggish, particularly with giant datasets or complicated workflows. Whereas not a serious concern, slower response occasions can concern some customers.
What G2 customers like about Salesforce Platform:
“As a consumer, what I do not like about Salesforce is that it is extremely costly, particularly for small companies and startups. As a developer, when you find yourself coping with giant quantities of knowledge, the reviews and dashboard can run slowly, and generally, the governor restrict can limit the complicated operation.”
– Salesforce Platform Evaluation, Dhruv G.
IAM controls who will get entry, whereas community monitoring instruments assist monitor what occurs inside your techniques. Right here’s my analysis of the perfect choices.
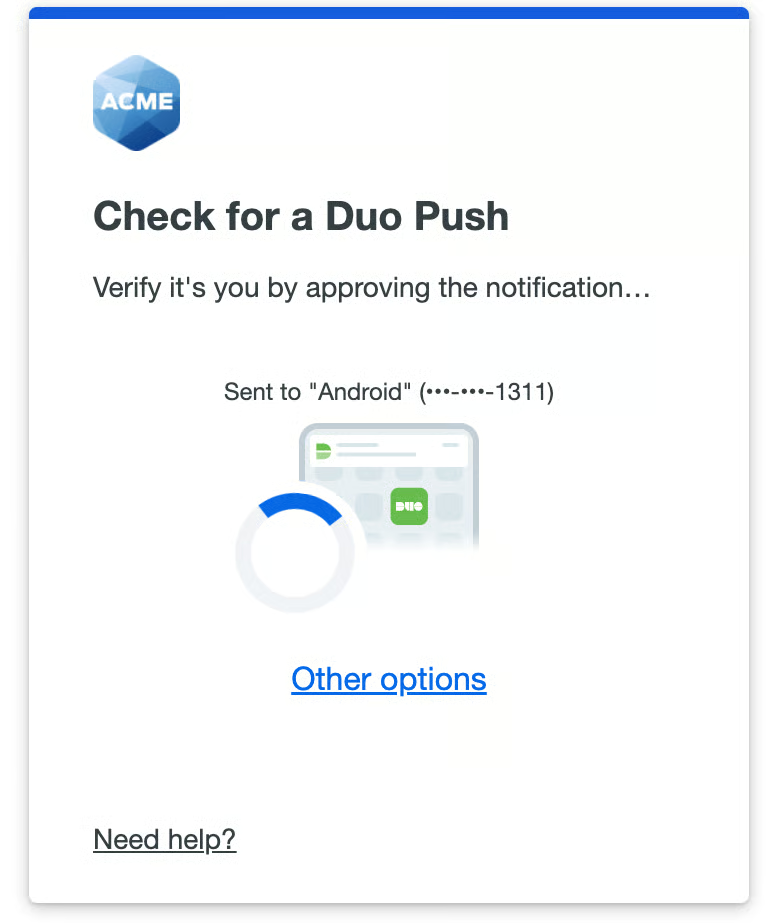
5. Cisco Duo: Greatest for easy, safe MFA and SSO
I’ve observed that G2 customers typically reward Cisco Duo for its easy method to safety. Many reviewers spotlight its simplicity and effectiveness, particularly concerning MFA, SSO, and adaptive authentication.
In contrast to some IAM instruments that really feel overloaded with pointless options, Duo stands out for maintaining issues centered and straightforward to handle, which is a constant theme in consumer suggestions.
From what I’ve seen, adverse suggestions tends to concentrate on the training curve of different IAM platforms. A number of customers have expressed that Duo is far simpler to make use of than different IAM instruments, which regularly have steep studying curves. Duo’s ease of use is continuously talked about, with customers appreciating its easy interface and its flexibility by way of integration with numerous purposes and platforms.
I’ve come throughout suggestions on G2 round Duo’s offline entry. Many customers have identified that its offline performance is proscribed, which may be an inconvenience in sure situations. Whereas Duo provides sturdy core options, some customers really feel this facet may very well be improved for higher flexibility in offline environments.
I’ve learn a number of reviewers point out struggles with the consumer interface and design. Whereas the system is useful, many G2 customers imagine the UI may very well be extra intuitive and fashionable. This suggestions means that whereas Duo is efficient, its design may very well be a barrier for customers who worth a extra streamlined, user-friendly expertise.
Regardless of these challenges, many G2 customers discover Duo to be a stable alternative for organizations looking for dependable MFA and SSO options.
For small IT groups, Duo typically emerges as the perfect IAM software program for small companies due to its free tier and straightforward deployment. Customers respect the chance to check Duo’s options with as much as 10 customers without charge, giving smaller groups or startups an inexpensive choice to implement safe entry controls.
What I like about Cisco Duo:
- I’ve observed that G2 customers respect how Duo retains issues easy — deploying MFA and SSO with out pointless complexity, not like another IAM instruments.
- I’ve learn a number of reviewers point out how a lot they get pleasure from Duo Passport, which remembers machine classes throughout apps, making entry smoother whereas sustaining tight safety.
What G2 customers like about Cisco Duo:
“It was easy to arrange, and authentication is nearly fast when connecting to my firm’s VPN. I desire the push notification approval method, because it solely requires me to faucet a button on my cellphone. It combines with many different out-of-the-box options, and it provides cloud-based, AD-integrated SAML SSO and digital equipment options to guard even bespoke interfaces.
We utilized Duo to guard our VMware Horizon desktop surroundings; setup and deployment had been easy, and I like how easy it’s to attach with Energetic Listing. Even higher, finish consumer onboarding was easy, and finish customers discovered the system easy to make use of, which is an important profit.”
– Cisco Duo Evaluation, Connie B.
What I dislike about Cisco Duo:
- Primarily based on my research of G2 opinions, offline authentication in Duo is proscribed, which generally is a drawback for customers in low-connectivity areas or frequent vacationers.
- I’ve observed that the UI feels outdated, and plenty of G2 customers recommend a refresh to make it extra fashionable and intuitive, particularly for IT groups dealing with giant deployments.
What G2 customers dislike about Cisco Duo:
“The setup of on-line and offline may be complicated for finish customers. Additionally, if time desyncs, it turns into an enormous drawback.”
– Cisco Duo Evaluation, Jonathan M.
Discover the finest password managers which are designed to securely retailer, generate, and autofill passwords whereas defending consumer accounts.
Now, there are just a few extra choices, as talked about beneath, that did not make it to this record however are nonetheless price contemplating, in my view:
- AWS Verified Entry: Greatest for securing AWS environments with Zero Belief entry controls.
- Google Cloud Id: Greatest for organizations deep within the Google ecosystem needing seamless IAM.
- Oracle Id Cloud Service: Greatest for hybrid cloud IAM with sturdy enterprise integrations.
- Rippling: Greatest for combining IAM with HR and payroll administration in a single platform.
- IBM Confirm: Greatest for AI-driven id safety and superior menace detection.
- SailPoint: Greatest for enterprise-level id governance and compliance administration.
Incessantly requested questions (FAQ) on IAM software program
1. Why is IAM necessary for companies?
IAM enhances safety, reduces the danger of knowledge breaches, streamlines consumer entry, and ensures compliance with trade laws (e.g., GDPR, HIPAA, SOC 2). It additionally improves productiveness by automating consumer provisioning and entry administration.
2. What options ought to I search for in IAM software program?
Key IAM options embody:
- Single sign-on (SSO): Allows customers to log in as soon as and entry a number of purposes.
- Multi-factor authentication (MFA): Provides an additional layer of safety past passwords.
- Person provisioning and de-provisioning: Automates account creation and elimination.
- Function-based entry management (RBAC): Assigns permissions primarily based on job roles.
- Audit and compliance reporting: Helps monitor entry logs for safety and regulatory functions.
- Id federation: Helps cross-domain authentication.
3. What’s the distinction between IAM and PAM (Privileged Entry Administration)?
IAM focuses on managing entry for all customers in a corporation. PAM is particularly designed to safe entry for privileged accounts with elevated permissions, reminiscent of system directors.
4. Is IAM software program cloud-based or on-premises?
IAM options may be:
- Cloud-based: Hosted by a supplier, scalable, and superb for contemporary SaaS purposes.
- On-premises: Put in inside an organization’s infrastructure, providing extra management over safety insurance policies.
- Hybrid: Combines each fashions for flexibility.
5. Can IAM software program assist with Zero Belief safety?
Sure, IAM is a crucial element of Zero Belief by implementing id verification, least privilege entry, and steady monitoring to forestall unauthorized entry.
6. How a lot does IAM software program price?
IAM pricing varies primarily based on options, deployment kind, and the variety of customers. Some distributors supply subscription-based fashions, whereas others present enterprise licensing. Extra prices might embody implementation, assist, and compliance options.
7. How can I select the proper IAM resolution for my enterprise?
Contemplate: Your group’s measurement and safety want Integration capabilities along with your current instruments, Compliance necessities, Scalability, ease of use, and Assist for contemporary safety practices (e.g., Zero Belief, MFA, adaptive authentication).
8. Which is the perfect id and entry administration software program?
One of the best IAM device is determined by your group’s wants, price range, and current infrastructure. Fashionable IAM options embody Okta, Microsoft Entra ID (previously Azure AD), JumpCloud, Cicso Duo, Ping Id, IBM Safety Confirm, and ForgeRock. It is best to check options, integrations, and safety capabilities earlier than selecting.
9. What’s the finest IAM resolution for mid-sized tech corporations?
JumpCloud and Okta typically stand out, providing flexibility throughout working techniques, SaaS integrations, and cloud environments with out overwhelming IT groups.
10. Which IAM software program is finest for small companies or startups?
Cisco Duo is without doubt one of the most dependable id entry apps for startups due to its ease of use and free plan. JumpCloud additionally works nicely for small companies that want machine administration alongside IAM.
12. What’s the best-reviewed IAM service for company environments?
In line with G2 opinions, Microsoft Entra ID and Okta constantly rank because the best-reviewed IAM platforms for company environments, balancing enterprise-grade safety with scalability.
13. What’s the most dependable id entry app for startups?
Cisco Duo typically ranks as essentially the most dependable id entry app for startups, due to its intuitive setup, sturdy MFA and SSO assist, and a beneficiant free tier for small groups.
14. Which IAM platform is finest for managing consumer roles?
Okta and Microsoft Entra ID each excel at role-based entry management (RBAC), providing granular permission administration, attribute-based guidelines, and just-in-time provisioning to assist organizations implement least-privilege entry effectively.
IAM prepared
After digging into the perfect IAM software program options, I’ve come to at least one conclusion: safety ought to work with individuals, not in opposition to them. Even when organizations spend money on IAM, adoption isn’t assured. G2 information exhibits the common consumer adoption charge is simply 71% — which means practically one in three workers nonetheless don’t totally use their IAM instruments. That hole creates not solely safety dangers but in addition productiveness bottlenecks.
So the true problem isn’t simply shopping for IAM software program — it’s discovering an answer that really works in follow for you, with out including complexity to each day operations.
The strongest authentication insurance policies on the earth received’t assist if workers discover methods round them out of frustration. On the similar time, a simple login expertise means nothing if the improper particular person positive factors entry. That’s the balancing act each IT and safety group faces, and the proper IAM device makes all of the distinction.
If your organization is deep in Microsoft’s ecosystem, Entra ID is a robust alternative. JumpCloud and Okta provide you with flexibility throughout completely different platforms. Salesforce Id is smart if Salesforce runs your small business, and Cisco Duo retains issues easy with sturdy MFA and integrations. Every device has its place, however the perfect IAM resolution is the one that matches how your group really operates.
On the finish of the day, IAM isn’t nearly securing logins — it’s about defending your small business from actual threats whereas maintaining entry clean for the proper individuals. So, decide the proper IAM, and also you’re not simply implementing insurance policies — you’re constructing a safety tradition that really works.
Nonetheless on the hunt? Discover our classes of id administration techniques to seek out the perfect match in your safety wants.